What are the latest CompTIA CySA+ CS0-001 exam tips? Get the latest exam questions online practice tests. “CompTIA CSA+ Certification Exam” CS0-001 exam. Get the full CompTIA CS0-001 exam dump: https://www.leads4pass.com/cs0-001.html (full exam dump)
CompTIA CS0-001 Exam pdf
[PDF Q1-Q13] Free CompTIA CS0-001 pdf dumps download from Google Drive: https://drive.google.com/open?id=12bDLt4RpVo-n208P4ythweIUbm-pW2jB
CompTIA CySA+: https://www.comptia.org/certifications/cybersecurity-analyst
The CompTIA Cybersecurity Analyst (CySA+) certification verifies that successful candidates have the knowledge and skills required to configure and use threat detection tools, perform data analysis and interpret the results to identify vulnerabilities, threats, and risks to an organization, with the end goal of securing and protecting applications and systems within an organization.
Latest CompTIA CS0-001 Online Exam Practice Questions
QUESTION 1
An investigation showed a worm was introduced from an engineer\\’s laptop. It was determined the company does not
provide engineers with company-owned laptops, which would be subject to company policy and technical controls.
Which of the following would be the MOST secure control implement?
A. Deploy HIDS on all engineer-provided laptops, and put a new router in the management network.
B. Implement role-based group policies on the management network for client access.
C. Utilize a jump box that is only allowed to connect to clients from the management network.
D. Deploy a company-wide approved engineering workstation for management access.
Correct Answer: D
QUESTION 2
A security analyst is creating baseline system images to remediate vulnerabilities found in different operating systems.
Each image needs to be scanned before it is deployed. The security analyst must ensure the configurations match
industry standard benchmarks and the process can be repeated frequently. Which of the following vulnerability options
would BEST create the process requirements?
A. Utilizing an operating system SCAP plugin
B. Utilizing an authorized credential scan
C. Utilizing a non-credential scan
D. Utilizing a known malware plugin
Correct Answer: A
QUESTION 3
A security analyst is performing a review of Active Directory and discovers two new user accounts in the accounting
department. Neither of the users has elevated permissions, but accounts in the group are given access to the
company\\’s sensitive financial management application by default. Which of the following is the BEST course of
action?
A. Follow the incident response plan for the introduction of new accounts
B. Disable the user accounts
C. Remove the accounts\\’ access privileges to the sensitive application
D. Monitor the outbound traffic from the application for signs of data exfiltration
E. Confirm the accounts are valid and ensure role-based permissions are appropriate
Correct Answer: E
QUESTION 4
A cybersecurity analyst traced the source of an attack to compromised user credentials. Log analysis revealed that the
attacker successfully authenticated from an unauthorized foreign country. Management asked the security analyst to
research and implement a solution to help mitigate attacks based on compromised passwords. Which of the following
should the analyst implement?
A. Self-service password reset
B. Single sign-on
C. Context-based authentication
D. Password complexity
Correct Answer: C
QUESTION 5
The human resources division is moving all of its applications to an IaaS cloud. The Chief Information Officer (CIO) has
asked the security architect to design the environment securely to prevent the IaaS provider from accessing its data-atrest and data-in-transit within the infrastructure. Which of the following security controls should the security architect
recommend?
A. Implement a non-data breach agreement
B. Ensure all backups are remote outside the control of the IaaS provider
C. Ensure all of the IaaS provider\\’s workforce passes stringent background checks
D. Render data unreadable through the use of appropriate tools and techniques
Correct Answer: D
QUESTION 6
A computer has been infected with a virus and is sending out a beacon to command and control server through an
unknown service. Which of the following should a security technician implement to drop the traffic going to the command
and control server and still be able to identify the infected host through firewall logs?
A. Sinkhole
B. Block ports and services
C. Patches
D. Endpoint security
Correct Answer: A
Reference: https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-DNS-Sinkhole/ta-p/58891
QUESTION 7
Which of the following systems or services is MOST likely to exhibit issues stemming from the Heartbleed vulnerability
(Choose two.)
A. SSH daemons
B. Web servers
C. Modbus devices
D. TLS VPN services
E. IPSec VPN concentrators
F. SMB service
Correct Answer: DE
QUESTION 8
A cybersecurity analyst is completing an organization\\’s vulnerability report and wants it to reflect assets accurately.
Which of the following items should be in the report?
A. Processor utilization
B. Virtual hosts
C. Organizational governance
D. Log disposition
E. Asset isolation
Correct Answer: B
QUESTION 9
A SIEM alert occurs with the following output: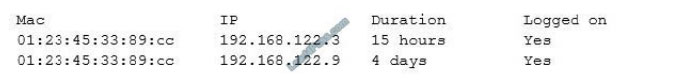
Which of the following BEST describes this alert?
A. The alert is a false positive; there is a device with dual NICs
B. The alert is valid because IP spoofing may be occurring on the network
C. The alert is a false positive; both NICs are of the same brand
D. The alert is valid because there may be a rogue device on the network
Correct Answer: B
QUESTION 10
Creating a lessons learned report following an incident will help an analyst to communicate which of the following
information? (Select TWO)
A. Root cause analysis of the incident and the impact it had on the organization
B. Outline of the detailed reverse engineering steps for management to review
C. Performance data from the impacted servers and endpoints to report to management
D. Enhancements to the policies and practices that will improve business responses
E. List of IP addresses, applications, and assets
Correct Answer: AD
QUESTION 11
A security analyst is performing ongoing scanning and continuous monitoring of the corporate datacenter. Over time,
these scans are repeatedly showing susceptibility to the same vulnerabilities and an increase in new vulnerabilities on a
specific group of servers that are clustered to run the same application. Which of the following vulnerability management
processes should be implemented?
A. Frequent server scanning
B. Automated report generation
C. Group policy modification
D. Regular patch application
Correct Answer: D
QUESTION 12
An organization wants to remediate vulnerabilities associated with its web servers. An initial vulnerability scan has been
performed, and analysts are reviewing the results. Before starting any remediation, the analysts want to remove false
positives to avoid spending time on issues that are not actual vulnerabilities. Which of the following would be an
indicator of a likely false positive?
A. Reports show the scanner compliance plug-in is out-of-date.
B. Any items labeled `low\\’ are considered informational only.
C. The scan result version is different from the automated asset inventory.
D. `HTTPS\\’ entries indicate the web page is encrypted securely.
Correct Answer: B
QUESTION 13
A company has recently launched a new billing invoice website for a few key vendors. The cybersecurity analyst is
receiving calls that the website is performing slowly and the pages sometimes time out. The analyst notices the website
is receiving millions of requests, causing the service to become unavailable. Which of the following can be implemented
to maintain the availability of the website?
A. VPN
B. Honeypot
C. Whitelisting
D. DMZ
E. MAC filtering
Correct Answer: C
Share leads4pass discount codes for free

About leads4pass!
leads4pass offers the latest exam exercise questions for free! CompTIA exam questions are updated throughout the year.
leads4pass has many professional exam experts! Guaranteed valid passing of the exam! The highest pass rate, the highest cost-effective!
Help you pass the exam easily on your first attempt.
Summarize:
AllaboutExams shares the latest CompTIA CySA+ CS0-001 exam dumps, CS0-001 pdf, CS0-001 exam exercise questions for free. You can improve your skills and exam experience online to get complete exam questions and answers guaranteed to pass the exam we recommend leads4pass CS0-001 exam dumps
Latest update leads4pass CS0-001 exam dumps: https://www.leads4pass.com/cs0-001.html (414 Q&As)
[Q1-Q13 PDF] Free CompTIA CS0-001 pdf dumps download from Google Drive: https://drive.google.com/open?id=12bDLt4RpVo-n208P4ythweIUbm-pW2jB